Configure GitLab as an Identity Provider in ZITADEL
This guides shows you how to connect GitLab as an identity provider in ZITADEL.
In ZITADEL you can connect an Identity Provider (IdP) like GitLab to your instance and provide it as default to all organizations. Also, you can register the IdP to a specific organization only. If you allow so, your organizations members can do the same in self-service.
GitLab Configuration
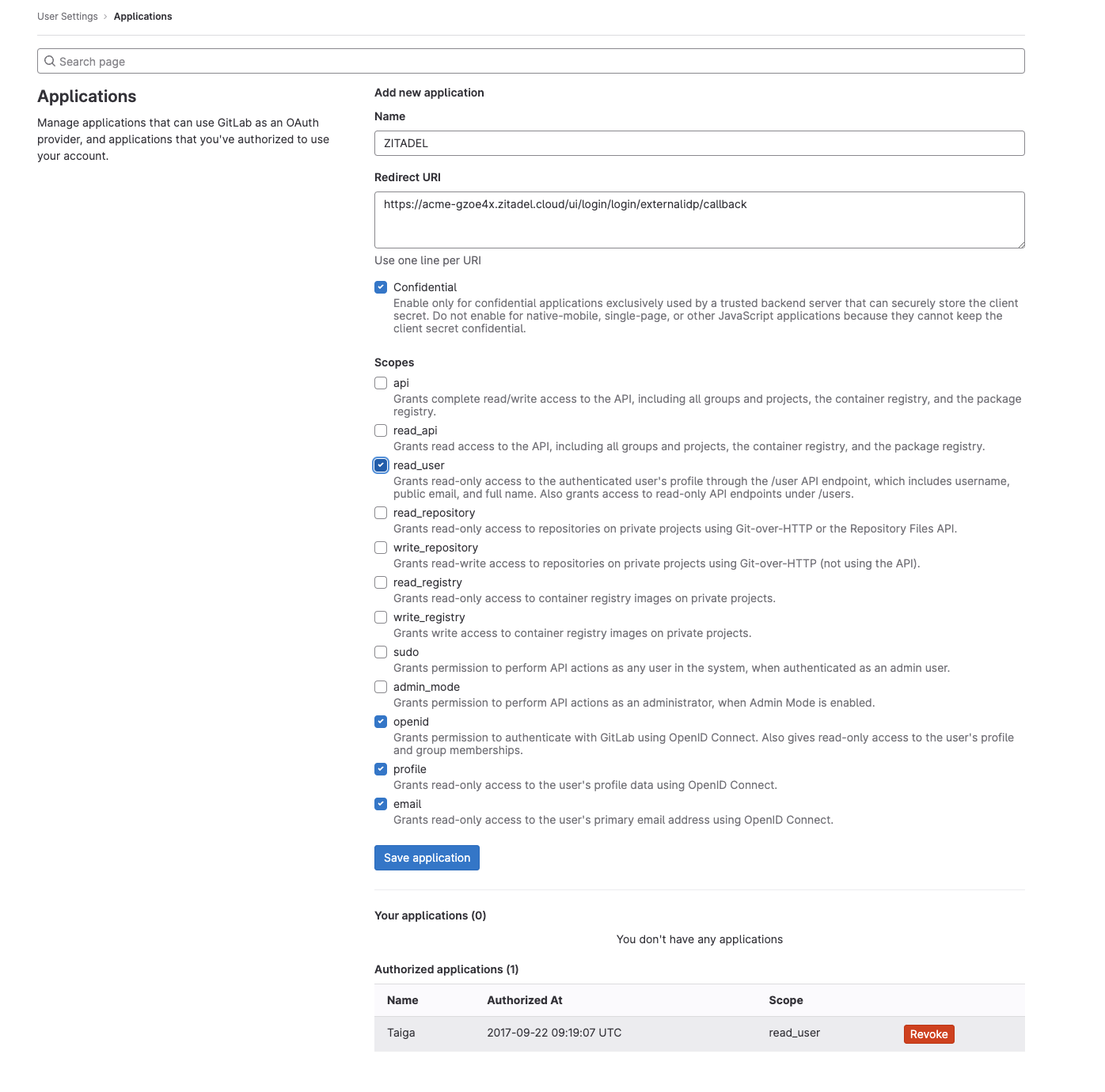
Register a new application
- Login to gitlab.com
- Select Edit Profile
- Click on Applications in the side navigation
For GitLab Self-Hosted go to your GitLab self-hosted instance and follow the same steps as for GitLab.
Fill in the application name.
You have to add the redirect URI, where GitLab should redirect, after the user has authenticated.
In this example our test instance has the domain https://acme-gzoe4x.zitadel.cloud.
This results in the following redirect URI:
https://acme-gzoe4x.zitadel.cloud/ui/login/login/externalidp/callback
To adapt this for you setup just replace the domain
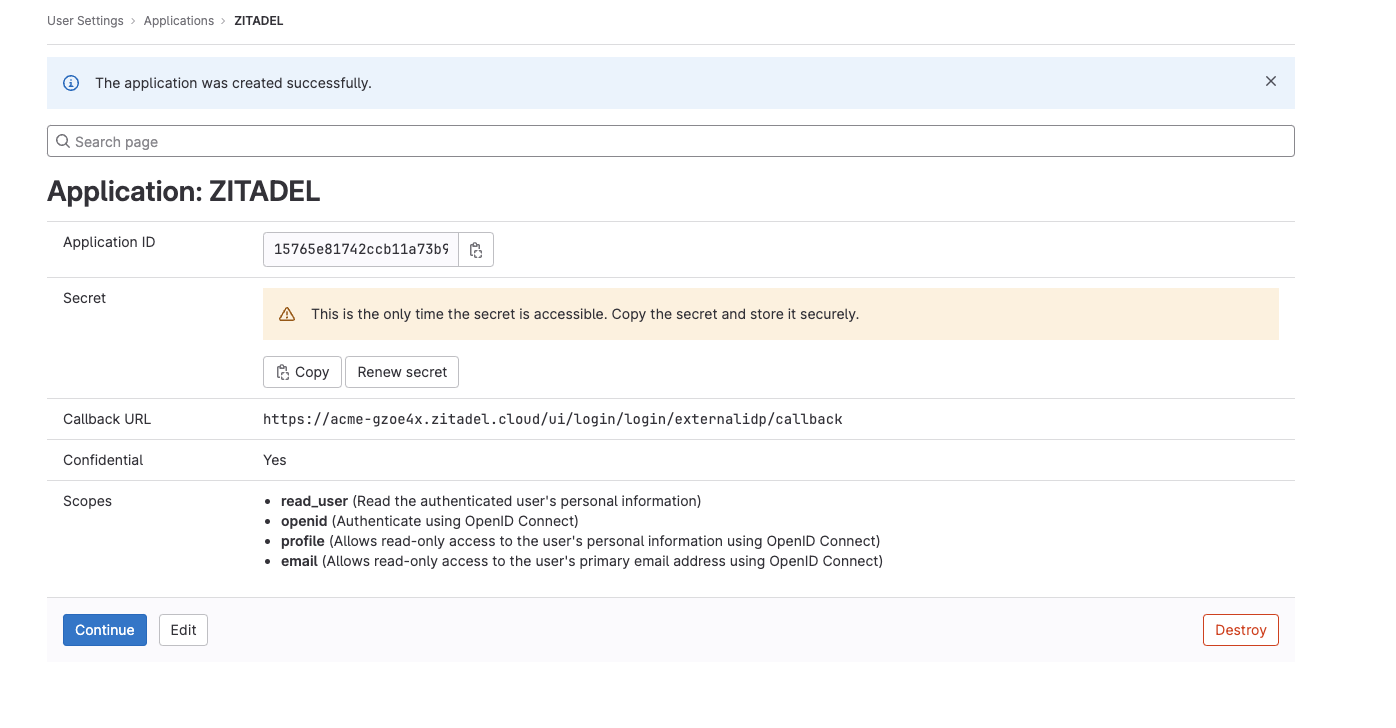
Client ID and Secret
After clicking "Save application", you will see the detail page of the application you have just created. To be able to connect GitLab to ZITADEL you will need a client ID and a client secret. Save the ID and the Secret, you will not be able to copy the secret again, if you lose it you have to generate a new one.
ZITADEL Configuration
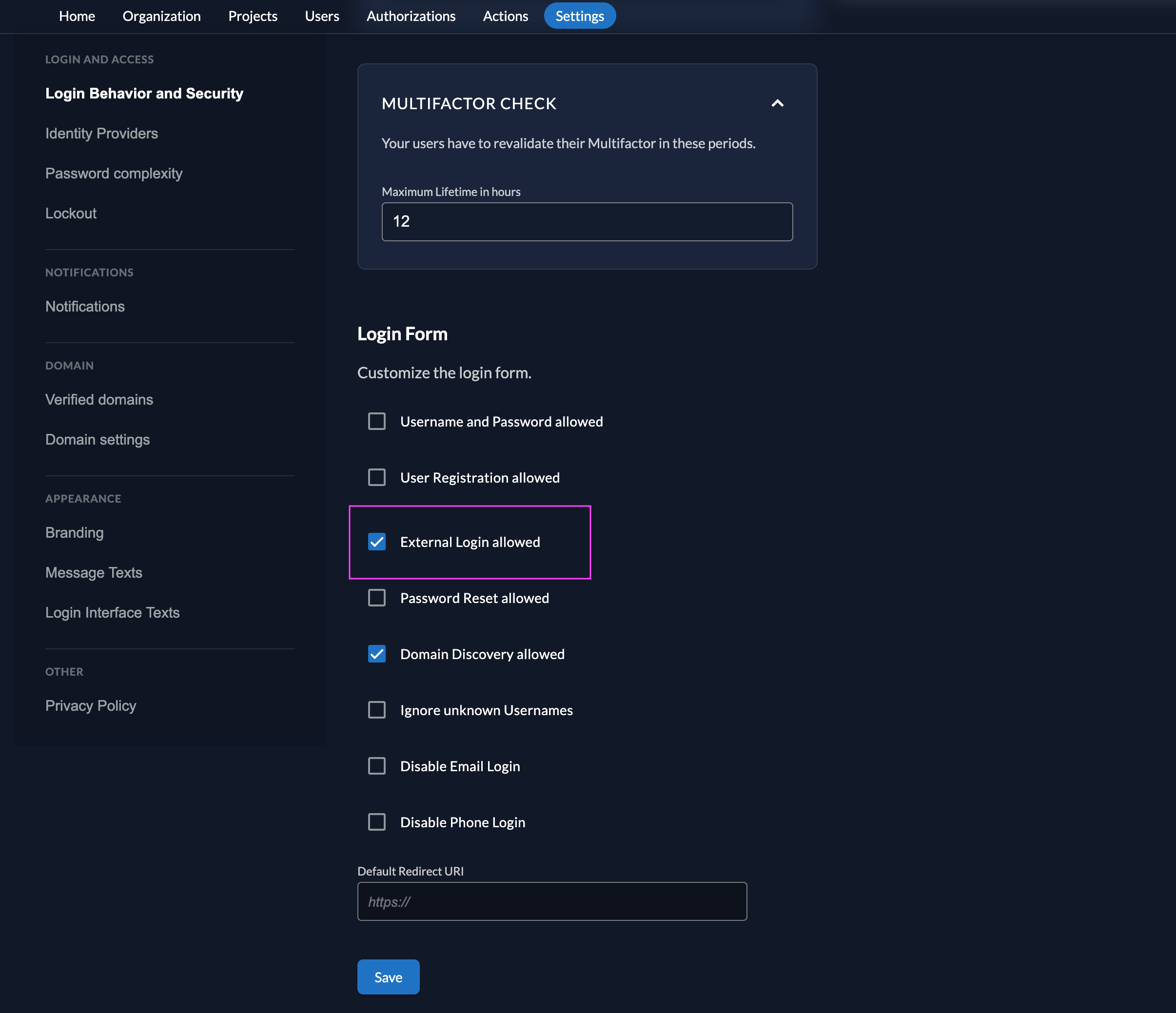
Add custom login policy
The login policy can be configured on two levels. Once in the default settings and this can be overwritten for each organization. The only difference is where you configure it. Go either to the settings page of a specific organization or to the default settings page. Default Settings: $YOUR-DOMAIN/ui/console/instance?id=general Organization: Choose the organization in the menu and go to $YOUR-DOMAIN/ui/console/org-settings?id=login
- Go to the Settings
- Modify your login policy in the menu "Login Behavior and Security"
- Enable the attribute "External Login allowed"
You can also change the settings through the API directly either in the default settings or on a specific organization:
Go to the IdP Providers Overview
Go to the settings page of your instance or organization and choose "Identity Providers".
In the table you can see all the providers you have configured. Also, you see all provider templates that are available.
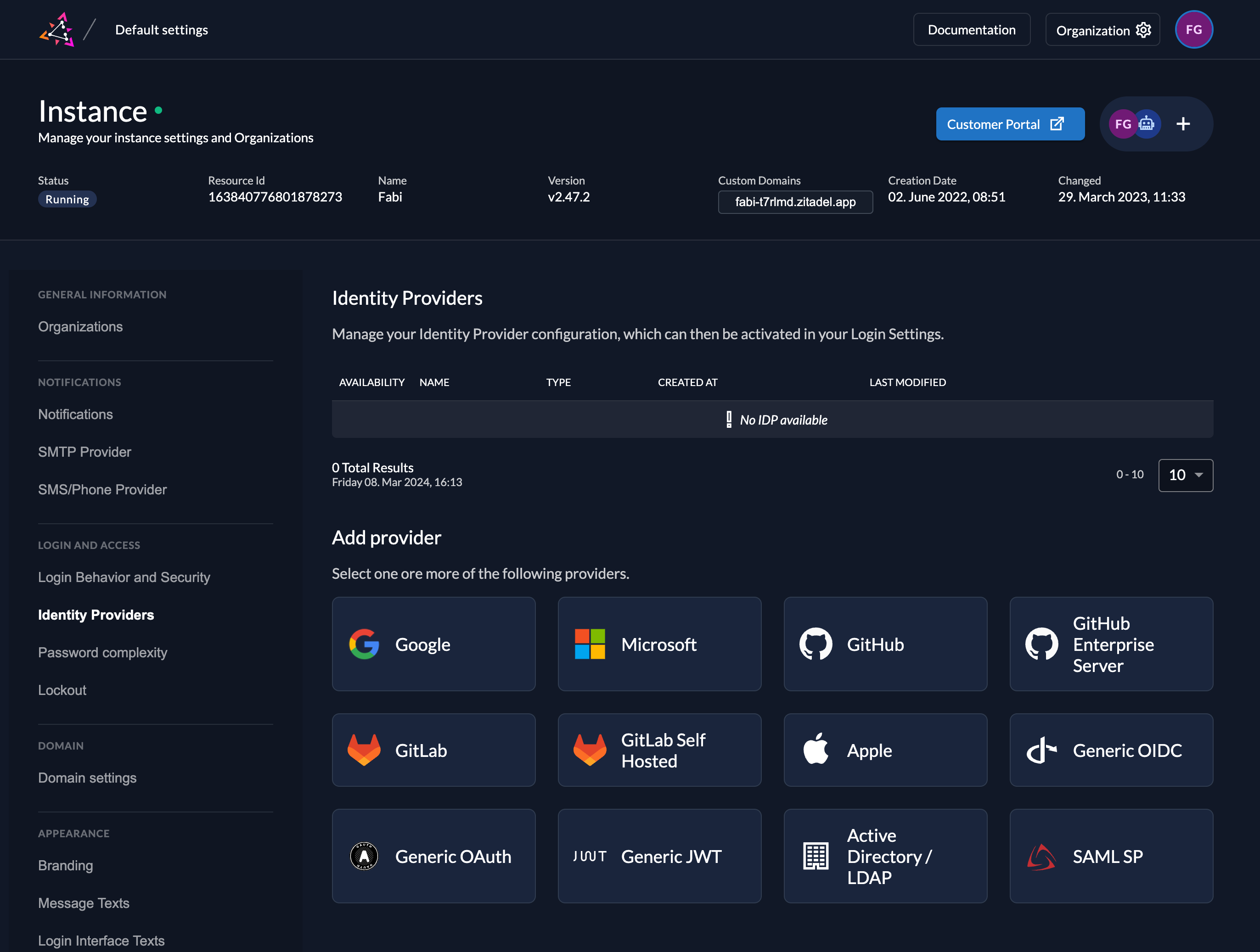
Select the GitLab or GitLab Self Hosted Provider template.
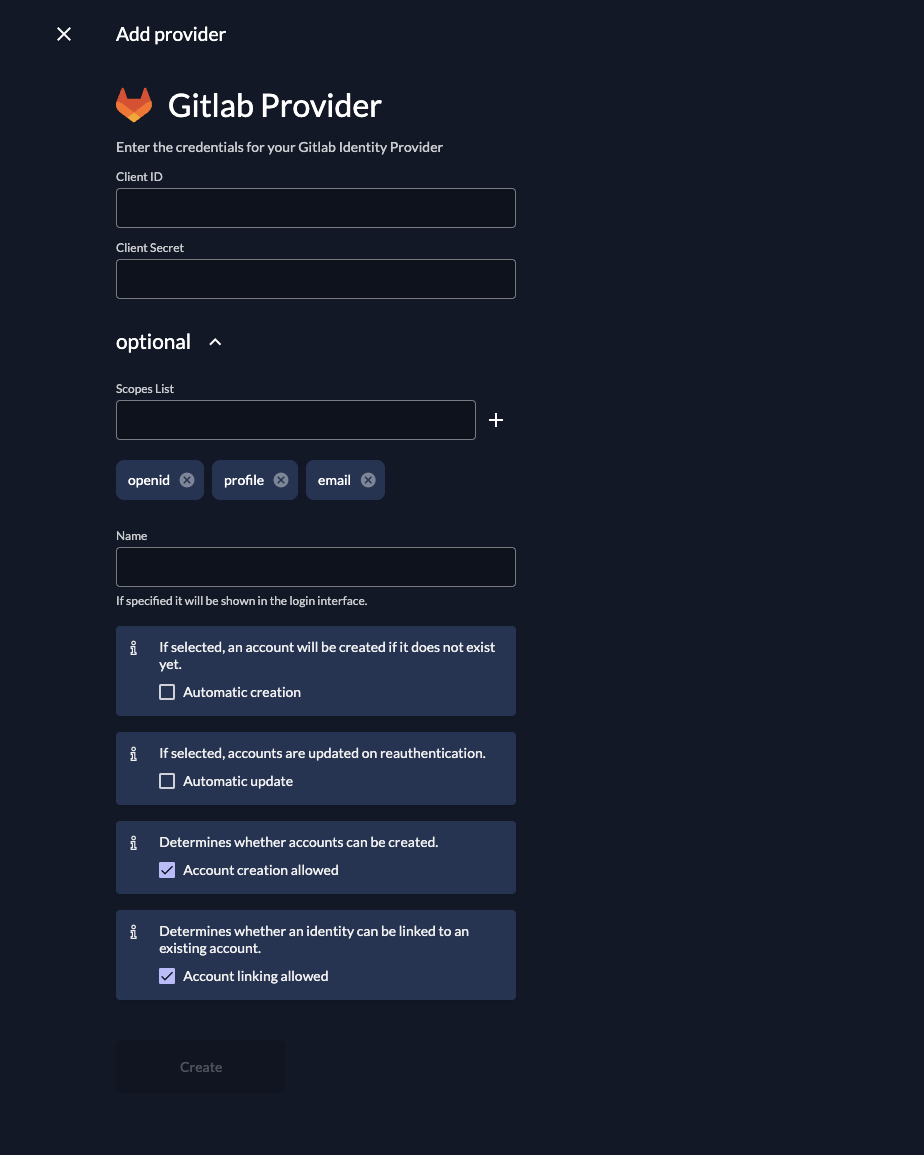
Create a new GitLab Provider
The GitLab provider templates have everything you need preconfigured. Add the client ID and secret you have created in the Gitlab Application.
You can configure the following settings if you like, a useful default will be filled if you don't change anything:
Scopes: The scopes define which scopes will be sent to the provider, openid, profile, and email are prefilled. This informations will be taken to create/update the user within ZITADEL. ZITADEL ensures that at least the openid-scope is always sent.
Automatic creation: If this setting is enabled the user will be created automatically within ZITADEL, if it doesn't exist.
Automatic update: If this setting is enabled, the user will be updated within ZITADEL, if some user data is changed withing the provider. E.g if the lastname changes on the GitLab account, the information will be changed on the ZITADEL account on the next login.
Account creation allowed: This setting determines if account creation within ZITADEL is allowed or not.
Account linking allowed: This setting determines if account linking is allowed. When logging in with a GitLab account, a linkable ZITADEL account has to exist already.
Either account creation or account linking have to be enabled. Otherwise, the provider can't be used.
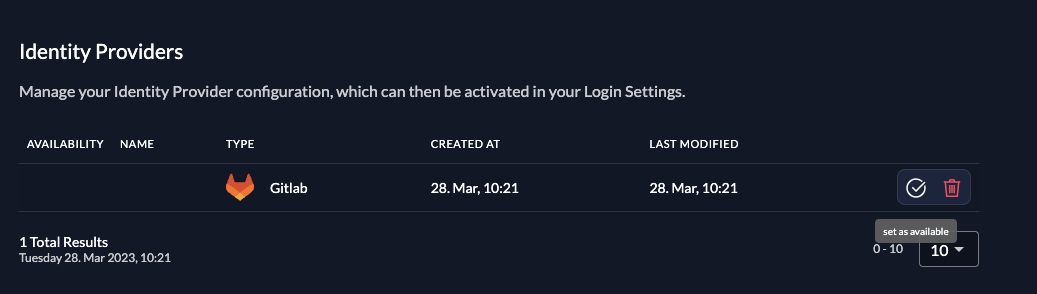
Activate IdP
Once you created the provider, it is listed in the providers overview. Activate it by selecting the tick with the tooltip set as available.
If you deactivate a provider, your users with links to it will not be able to authenticate anymore. You can reactivate it and the logins will work again.
The provider can also be activated via API. As the identity providers are sub-resources of the login settings, this is done by linking the provider to the settings:
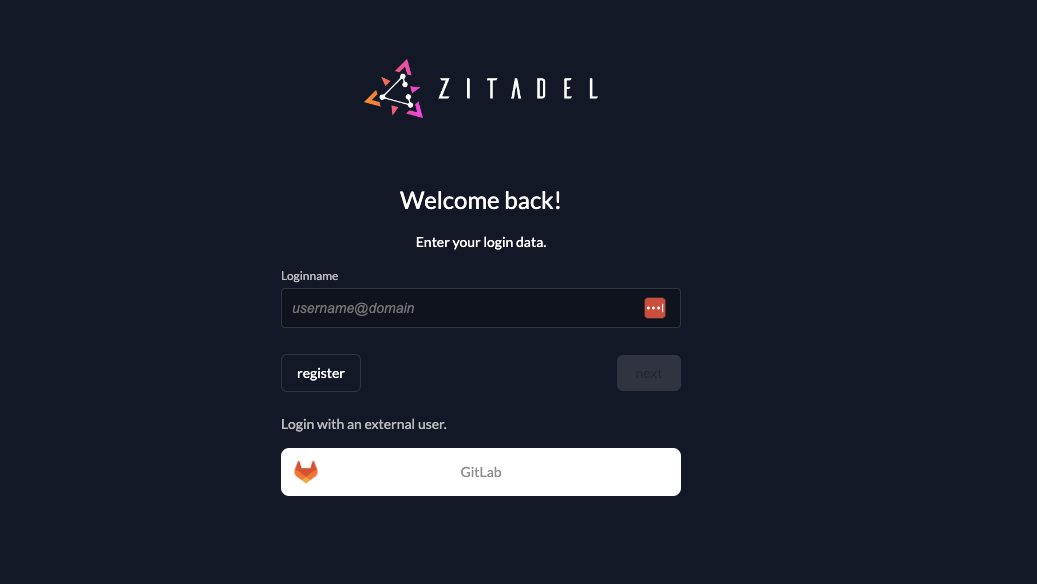
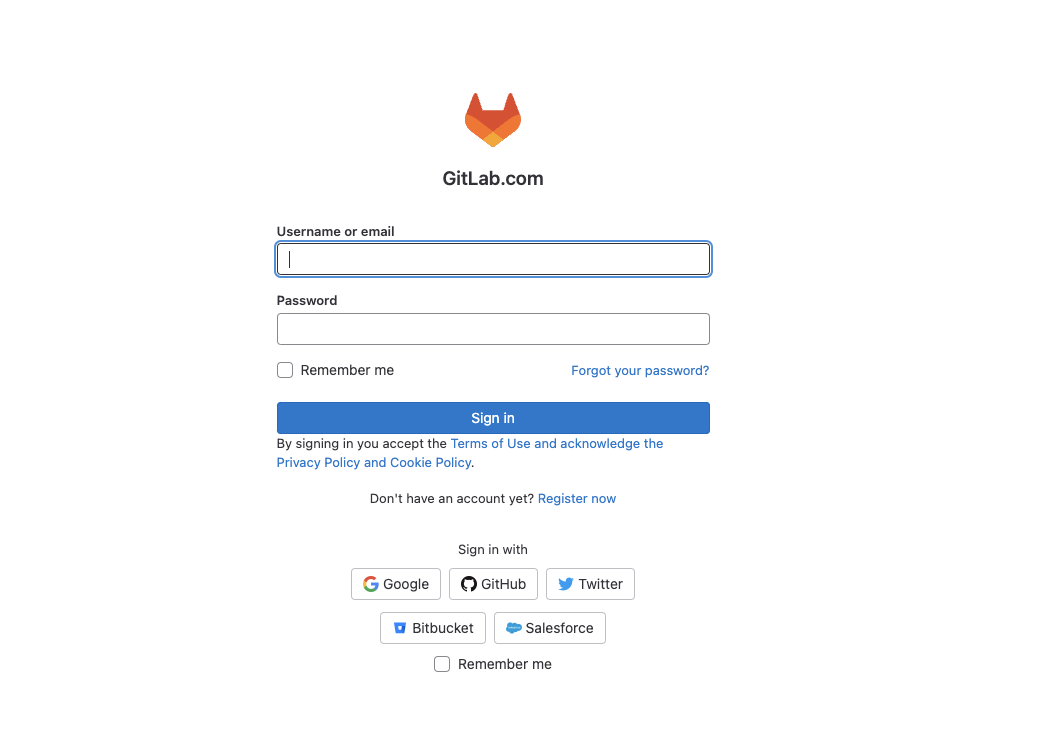
Test the setup
To test the setup, use incognito mode and browse to your login page. You see a new button which redirects you to your GitLab login screen.
By default, ZITADEL shows what you define in the default settings. If you overwrite the default settings for an organization, you need to send the organization scope in your auth request.
The organization scope looks like this: urn:zitadel:iam:org:id:{id}.
You can read more about the reserved scopes
or use the ZITADEL OIDC Playground to see what happens with the login when you send different scopes.
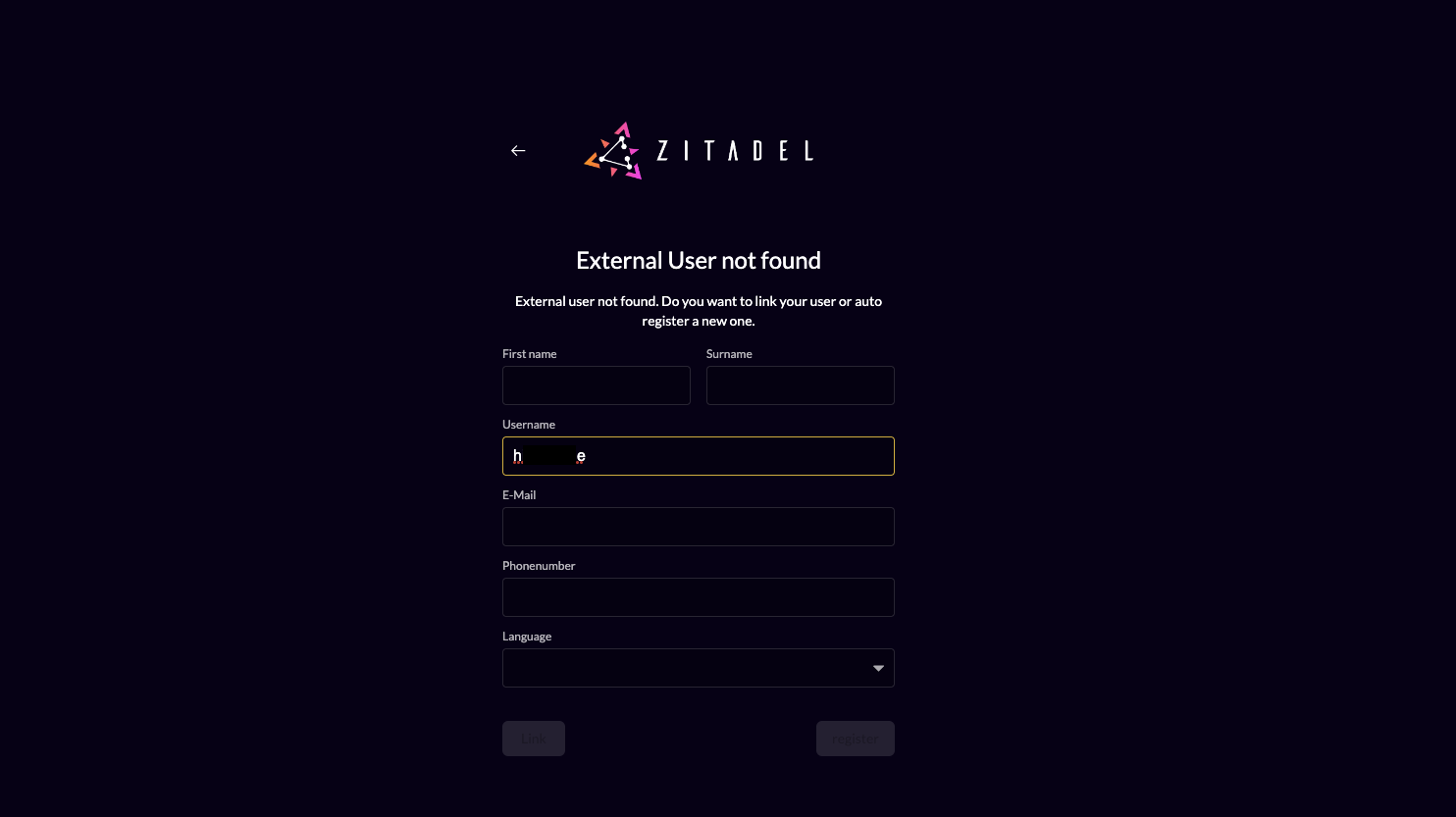
New unlinked users are presented with the screen below. GitLab is an OAuth provider and does not provide a standardized way to get the user data. This means that ZITADEL has no way to prefill the first and lastname fields.
Optional: Add ZITADEL action to autofill userdata
You can use a ZITADEL action if you want to prefill the fields firstname and lastname with GitLab data.
- Go to the users target organizations settings page.
- Add a new action with the body below. Make sure the action name equals the scripts function name. Also change the id in the script to match your provider configurations id.
- Add the action to the flow "External Authentication" and trigger it on "Post Authentication"
loading...